Internal policies exist to create predictability, reduce avoidable friction, and protect critical decisions from being made on the fly. The risk is not “having rules.” The risk is having policies that are unclear, contradictory, or hard to follow in real work.
When that happens, people stop treating policies as a shared reference and start treating them as noise. Teams invent workarounds, managers interpret differently, and employees spend more time decoding intent than doing the work. In larger organizations, the same confusion can turn into inconsistent decisions and audit headaches.
Why This Topic Gets Risky So Fast
Policy problems rarely look dramatic at first. They look like small delays: someone asks a “simple question,” a manager answers from memory, and an employee notices a mismatch between the written rule and the actual practice. Over time, that mismatch creates trust erosion and a culture where the “real policy” is who you ask.
Risk In One Sentence
If employees cannot quickly tell what a policy expects, when it applies, and who can override it, the policy becomes a source of inconsistent behavior instead of a stabilizer.
Common Wrong Assumptions
Assumption
- “If it’s written down, people will follow it.”
- “More detail means more clarity.”
- “One policy can cover all scenarios.”
- “If leaders agree, employees will interpret it the same way.”
- “Once published, the policy is done.”
What Often Happens Instead
- People follow the easiest interpretation, not the intended one.
- Extra detail hides the core decision employees need.
- Edge cases become exception chaos.
- Different teams create different local rules.
- Outdated policies keep circulating as “the link”.
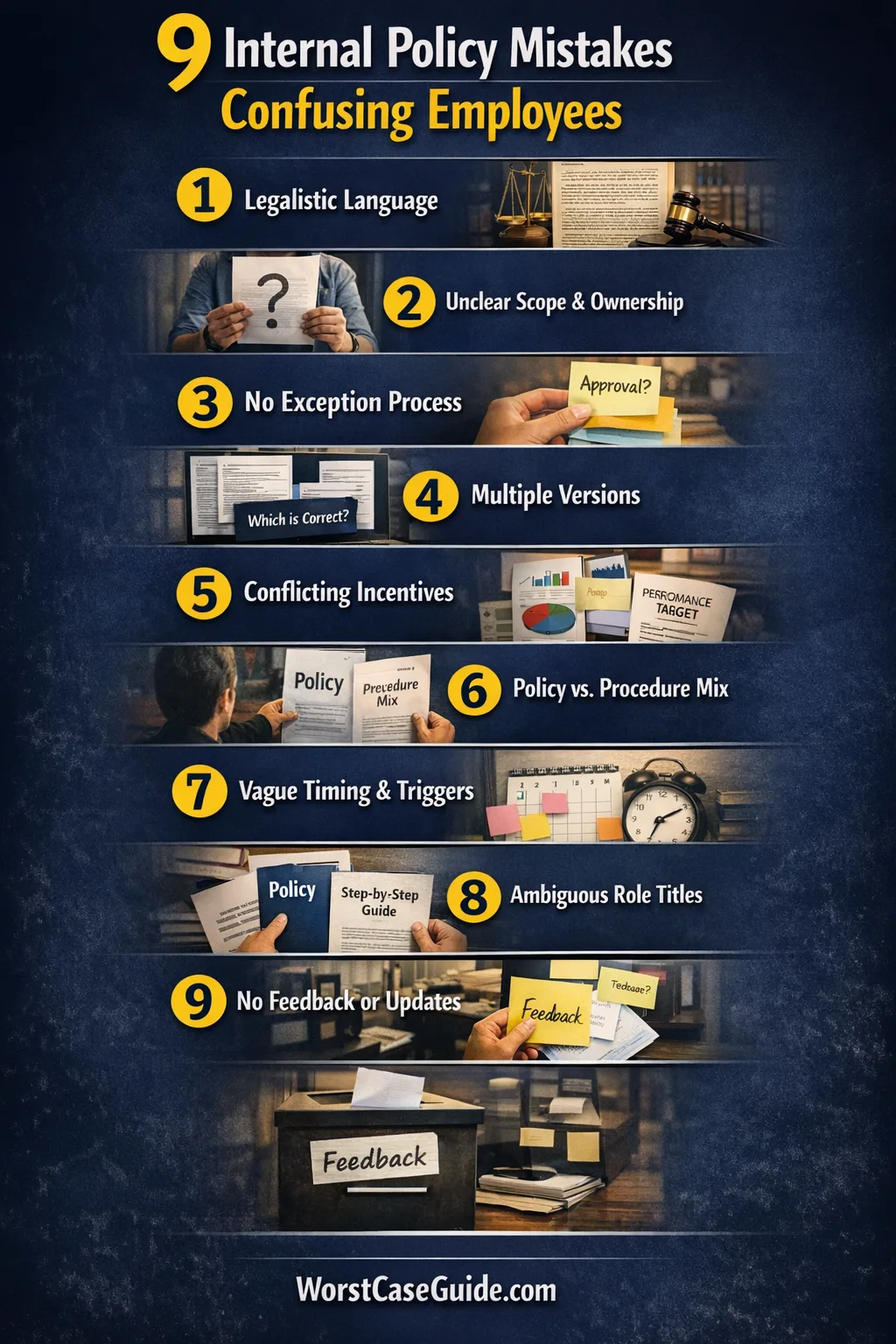
Internal Policy Mistakes That Confuse Employees
The mistakes below are written as practical failure modes. Each one tends to show up in small teams and scales into bigger damage as headcount, locations, or systems multiply.
| Mistake Pattern | What Employees Experience | Early Signal | Safer Direction |
|---|---|---|---|
| Legalistic writing | “I can’t tell what this means.” | Many clarifying questions | Plain language + examples |
| Version sprawl | “Which one is current?” | Multiple links in circulation | Single source + change log |
| No exception path | “Who can approve this?” | Ad-hoc manager approvals | Defined decision tree |
| Policy-procedure mix | “Is this required or optional?” | Debates about steps | Separate “rule” vs “how-to” |
Mistake 1: Writing Policies Like Contracts Instead Of Work Instructions
Why it happens: Policies get drafted to be “bulletproof,” so they inherit legal tone and dense wording. The document becomes optimized for formal defensibility rather than day-to-day understanding.
Early warning signs: Employees quote sentences back to managers, different readers reach different interpretations, and people avoid the policy unless forced. In smaller teams, it shows up as DM questions; in larger systems, it turns into inconsistent enforcement.
Worst-case outcome: The policy becomes a symbolic document that no one trusts, so decisions shift to informal approvals and “what worked last time.” That raises the chance of unequal treatment across teams.
Safer approach: A policy can stay formal without being opaque. Short sentences, defined terms, and a small “real examples” section often reduce confusion more than extra clauses. If the policy must include strict language, a plain-language companion view can carry the operational meaning.
Quick clarity test: If two managers can read the same paragraph and reasonably reach different decisions, the text is not functioning as a shared rule.
Mistake 2: Leaving Scope And Ownership Implicit
Why it happens: The author assumes “everyone knows” who the policy is for and who maintains it. Over time, teams change, roles shift, and the policy keeps its old assumptions. The result is orphaned governance.
Early warning signs: Questions like “Does this apply to contractors?” or “Is this for all regions?” show up repeatedly. People also ask who can interpret or update the policy, which is a sign of missing ownership.
Worst-case outcome: Different departments treat the policy as “someone else’s job,” so it becomes stale and selectively applied. Employees then learn that policy language is negotiable, which weakens consistency and escalates conflict.
Safer approach: Scope can be stated without turning the policy into a long taxonomy. A short “Applies to / Does not apply to” section, plus a named policy owner or owning function, usually reduces repeat questions. In larger organizations, a clear review cadence also signals that the policy is maintained, not abandoned.
Mistake 3: Not Defining An Exception Path
Why it happens: Many policies aim for simplicity and avoid discussing exceptions because exceptions feel like loopholes. Real work still produces edge cases, so exceptions happen anyway—just without structure.
Early warning signs: Employees learn that “asking the right person” works better than following the written rule. Approvals become invisible, and managers carry an unwritten playbook that differs by team.
Worst-case outcome: The policy gets enforced unevenly. That can create perceived unfairness, delays, and a paper trail that does not match reality. In higher-stakes workflows, it can also create approval bottlenecks because nobody knows who is allowed to say yes.
Safer approach: An exception path does not need to encourage exceptions. It can define the decision owner, the conditions that trigger review, and what gets documented. If you are in a smaller project, a simple “Ask X, record Y” pattern may be enough; in larger systems, a lightweight decision tree often reduces ad-hoc overrides.
Mistake 4: Creating Multiple “Sources Of Truth”
Why it happens: Policies get copied into onboarding docs, slide decks, chat pins, and team wikis. Each copy starts as helpful. After a few revisions, the organization has several versions with small differences, and nobody is sure which one is authoritative.
Early warning signs: People share “the policy link” and receive replies like “That’s outdated.” New hires get conflicting guidance from different documents and different managers. Teams begin adding disclaimers such as “I think this is current.”
Worst-case outcome: Employees follow different rules based on where they learned them. That produces process divergence, rework, and frustration. It also makes it hard to prove that decisions were made using a consistent standard.
Safer approach: A single canonical policy page with a visible revision date and a short change log tends to reduce confusion. Other docs can reference the rule without duplicating it, or they can embed a read-only excerpt that is clearly tied to the source. The safer goal is not “no repetition,” but controlled repetition.
Mistake 5: Policies That Conflict With Incentives And Metrics
Why it happens: A policy may be designed for risk reduction, while performance metrics reward speed, volume, or short-term output. Employees then face a quiet tradeoff: follow the policy or hit the target. In practice, the target often wins, and the policy becomes ceremonial.
Early warning signs: People describe the policy as “nice in theory” and talk about “what leadership really wants.” Managers selectively enforce rules during audits or incidents. A common signal is exception normalization under time pressure.
Worst-case outcome: Employees learn to treat policy compliance as optional until something goes wrong. That can lead to repeat incidents, uneven standards across teams, and difficult retrospectives where nobody can explain why the written rule was ignored.
Safer approach: Policies that survive real work often acknowledge tradeoffs explicitly. If you are in a fast-moving environment, a policy can define minimum guardrails and describe what “acceptable speed” looks like. In larger systems, aligning metrics with the policy’s intent reduces the silent conflict employees feel between compliance and performance.
Mistake 6: Mixing Policy With Procedure And Tool Steps
Why it happens: Policies sometimes try to be complete by including every step, screenshot, and tool instruction. Those details change faster than the rule itself, so the document becomes outdated even when the core policy remains valid. Employees then question the whole thing, including the non-negotiables.
Early warning signs: People debate whether a step is required or “just guidance.” Tool changes trigger policy edits, and the policy becomes hard to maintain. Another signal is employees asking, “Is this the rule or just one way to do it?”
Worst-case outcome: The policy becomes too long to read and too brittle to keep current. Employees follow workarounds or copy older steps from colleagues, which increases inconsistency and makes onboarding slower.
Safer approach: Separating “what must be true” (policy) from “how it’s usually done” (procedure) tends to reduce confusion. If you are in a smaller team, a short “Approved methods” section can work; in larger systems, a policy that references a maintained procedure page keeps the rule stable while allowing procedures to evolve without breaking meaning.
Mistake 7: Leaving Triggers And Timing Vague
Why it happens: Many policies describe what “should” happen but do not specify when the policy is triggered or which events start the clock. Without timing, the policy becomes open to interpretation, and employees default to whichever timeline feels least risky for them.
Early warning signs: People ask, “Does this apply before the project starts or after approval?” or “How soon do we need to report this?” Teams create their own deadlines, which leads to schedule mismatch and handoff friction.
Worst-case outcome: Critical actions happen too late, or they happen too early and create unnecessary delays. In cross-team work, the lack of timing produces missed dependencies and frustration because each team believed it was following the “same” policy.
Safer approach: Policies often become clearer with a small trigger list: “This applies when X happens.” A timing note like “within N business days” can reduce ambiguity without turning the policy into a calendar. If you are in a complex environment, adding a simple timeline example can prevent employees from guessing what the policy intended.
Mistake 8: Using Role Names That Do Not Match Reality
Why it happens: Policies are written using idealized roles (“Project Owner,” “Approver,” “Admin”) that do not map cleanly to real job titles, regional structures, or matrix organizations. Employees then have to translate the policy into their local context, which introduces inconsistent mapping.
Early warning signs: People ask who counts as the “owner” in their team. Two teams follow the policy differently because their role mapping is different. In fast-growing companies, this shows up as repeated role confusion during onboarding and handoffs.
Worst-case outcome: Accountability becomes unclear. Tasks get dropped because multiple people assumed someone else had the role, or work gets duplicated because nobody is confident who should act. In stricter workflows, the ambiguity can create approval gaps where actions occur without the intended review.
Safer approach: Policies tend to work better when roles are defined as responsibilities, not titles. A short “Role definitions” section (“the person accountable for X”) is often clearer than a label. If you are in a multi-region environment, including a note like “local equivalents” helps employees find the right counterpart without guessing.
Mistake 9: Publishing Without A Feedback Loop Or Change Discipline
Why it happens: Policy drafting focuses on getting to “published,” not on what happens afterward. Without a feedback channel, policies accumulate known pain points. Without change discipline, updates appear silently and employees discover them through surprises, not through communication.
Early warning signs: People rely on tribal knowledge, or they keep personal notes because the policy is unreliable. Employees say things like “It changed again?” Managers become the default help desk for policy interpretation, which is a sign that the policy is not functioning as a stable reference.
Worst-case outcome: The organization develops policy fatigue. People stop checking updates, and the policy’s authority collapses into a culture of exceptions. In regulated or high-accountability contexts, this can create a mismatch between “official policy” and documented practice.
Safer approach: A light feedback loop can be enough: a visible place to report confusion, plus a predictable review rhythm. A simple change log and a “what changed” note can reduce surprise. If you are in a smaller project, even a quarterly check can maintain trust; in larger systems, a named owner and consistent release notes reduce drift.
General Risk Patterns Behind These Mistakes
Across industries, policy confusion often comes from a small set of repeating patterns: ambiguity (unclear meaning), fragmentation (too many versions), misalignment (rules vs incentives), brittleness (policies tied to tools), and unowned maintenance (no feedback or review). These patterns show up in different clothes, but the employee experience is similar: uncertainty, extra coordination, and inconsistent outcomes.
A Practical Self-Check For Any Policy
- Can an employee tell, in under a minute, what the policy requires and what it allows?
- Is there one canonical location where the latest version lives?
- Do scope, roles, and triggers reduce guesswork rather than add it?
- Is the exception path defined, with a clear decision owner?
- Does the policy survive real incentives, or does it become theoretical under pressure?
FAQ
How long should an internal policy be?
Length tends to matter less than retrievability and decision clarity. If employees cannot quickly find the rule and understand its core intent, even a short policy can fail. Many teams keep the policy short and move step-by-step details into separate procedures.
What is the difference between a policy and a procedure?
A policy usually states what must be true (rules, constraints, responsibilities). A procedure usually explains how work is done (steps, tools, examples). When the two are blended, employees often lose track of what is mandatory versus what is just a common workflow.
How often should policies be reviewed?
Review cadence depends on how quickly the underlying work changes. A stable area may need only periodic review, while fast-moving areas benefit from more frequent checks. The key signal is whether employees regularly report confusion, find outdated steps, or rely on tribal knowledge instead of the written policy.
How can exceptions be handled without creating loopholes?
Many organizations reduce chaos by defining a narrow exception path: who decides, what conditions trigger review, and what gets recorded. This can keep exceptions visible and reduce informal overrides that vary by manager or team.
What if different teams truly need different rules?
When variation is real, confusion often comes from hidden differences. A common approach is to keep a shared baseline policy and explicitly document approved variations by scope (team, region, role). This makes the differences intentional rather than accidental, and keeps interpretation drift from spreading.
Where should policies live so employees can find them?
Employees tend to trust what is easy to find and consistently current. The safest pattern is usually a single canonical location with a visible revision date and a change log. Copies in other places tend to create version sprawl unless they are clearly marked as non-authoritative.
How can policy updates be introduced without surprising people?
Surprises often happen when changes are silent. A short release note describing what changed, why, and when the change takes effect can reduce confusion. Even a lightweight announcement and a maintained change history helps employees avoid learning updates through mistakes or conflicting instructions.
A) Internal Policy Mistakes That Confuse Employees
B) 9 Internal Policy Mistakes That Confuse Employees


